CloudFlex
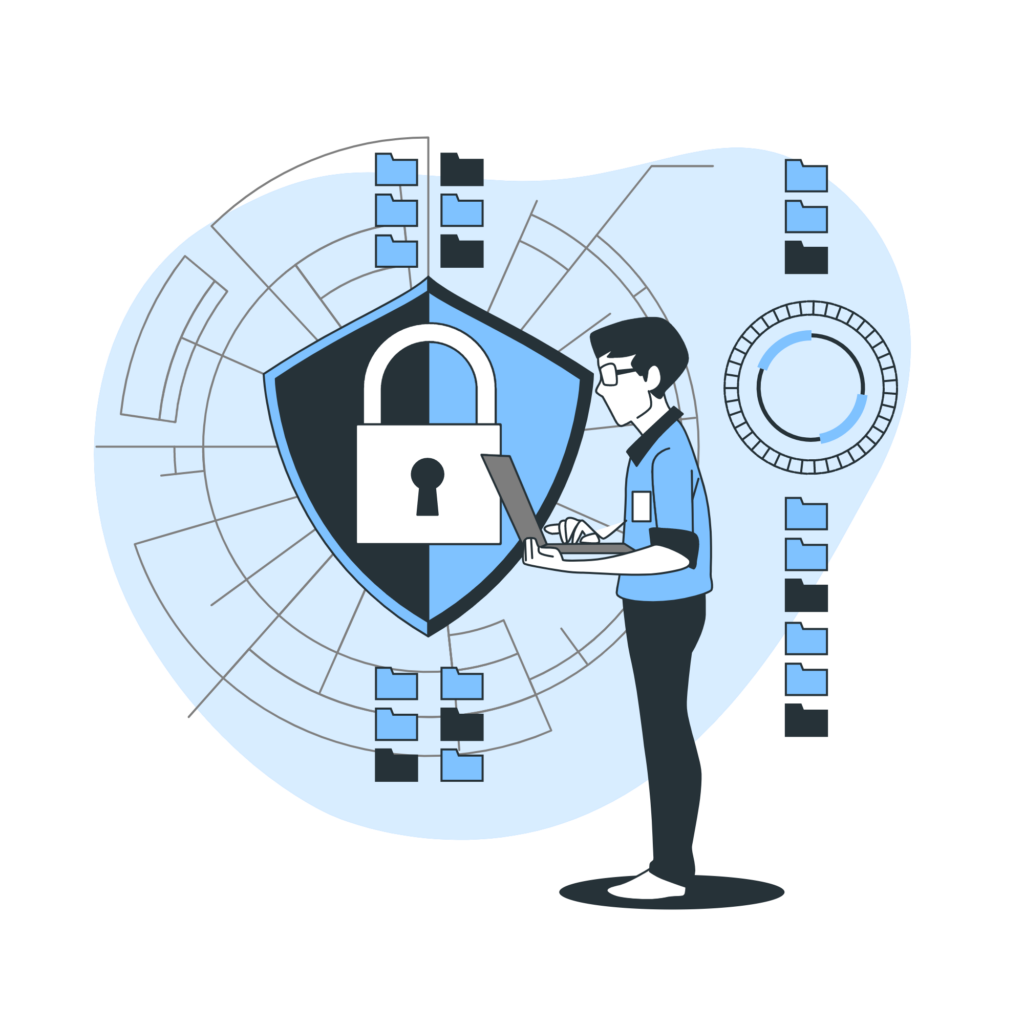
We care about your safety
CloudFlex
Information Security
Internet is the global meeting place for personal and business communication. The increasing use of internet and the decreasing cost of bandwidth has revolutionized the way the world does business on local and global level.
Internet also has given rise to number of problems associated with lack of control over Internet usage such as – loss of employee productivity, data leakage, bandwidth drainage, legal liability for unsafe surfing etc. Organization has to secure its IT infrastructure at Gateway,Server and Desktop levels through identity based security policies to mitigate these risks.
CloudFlex
UTM & Web Security
Single layered security such as a firewall or antivirus protection is no longer enough. The complexity involved in managing multiple such solutions has led to unified security with multiple features over a single platform – Unified Threat Management (UTM). UTM addresses vital concerns of organisations like : user identity, bandwidth management, business continuity, DLP, granular reporting etc.
Security solution is as good as it is configured and maintained over a period of time. The demand for information security & access policies is dynamic and keeps changing from time to time. Hence, organisation needs a reliable solution/service provider rather than a product supplier who can provide good post-installation support and work together for ever-changing security landscape..
Board Rooms
Auditoriums
Conference Rooms
Control Rooms
CloudFlex
VPN & Remote Access
Users are accessing more applications remotely than ever before. IPSec (Internet Protocol Security) based VPNs were originally developed over a decade ago to help businesses avoid the costs of privately-leased WAN links. IPSec needs compatible hardware or software at both locations. IPsec is an effective solution for site-to-site Virtual Private Networking, but it is severely limited solution for remote access.
Because they create a tunnel between two points, IPSec VPNs provide direct (non-proxied) access and full visibility to the entire network. Unless accompanied by an additional network security appliance, companies also face the possibility that hackers will use the remote IPSec VPN network tunnel to gain unauthorized access to the corporate network.

SSL VPNs are designed specifically to enable increased productivity for remote users by providing easy-to-use, secure remote access to applications. SSL works at the application layer instead of the network layer, providing the highly granular policy and access control needed for secure remote access. Because SSL is included in all modern browsers, SSL VPNs can empower today’s mobile workforce with client less remote access—while saving IT departments the headache of installing and managing the complexity of IPSec VPN clients.
Endpoint Security and Management
With more than 70% of corporate data residing on desktops/laptops – the desktop management has become a never-ending job for the IT dept. With increasing service requests and growth in the number of desktops – overall time spent towards this repetitive nature of work- kills the productivity of IT team. Statistics shows that companies worldwide spend nearly 60-70% of their IT budgets on desktop maintenance.
In order to counter this issue, organisations need Endpoint Management Suite (EMS) that can- not only handle virus & malware but also boost desktop performance and enhance employee productivity.
Enterprise security vendors are adapting to this changing landscape. Organisations are moving towards server or appliance based centralized deployment & integration with data loss prevention, device control and endpoint visibility & control features.

IDeploying security solution involves a tradeoff between cost and risk management. The task of choosing the right technical solution becomes complex and hence the differentiating factors to be considered are – Policies & management, ease of installation & configuration, impact on system performance, granular report and technical support.
Our integrated endpoint security solution helps you to prevent data loss and efficient management of IT assets while retaining business flexibility. In addition, organizations can meet regulatory and security compliance requirements.
User name and password is a dying security model to control access. Like the same model that account holders use today to get cash from an ATM, multi factor authentication replaces the use of a password with the combination of two or more of the following factors: USB token , SMART card , PIN or biometric fingerprint. By requiring two independent elements for user authentication , this approach significantly decreases the chances of unauthorized information access.